By: Jake Smiths
For years, cybersecurity strategy has revolved around a central belief: if organizations can identify which software vulnerabilities are being exploited in the wild, they can prioritize those weaknesses and reduce risk. Budgets, SLAs, and compliance frameworks were built on that logic. It worked when exploitation was slow, manual, and traceable.
It doesn’t work anymore.
Modern software is built on open source code. According to the 2025 Open Source Security and Risk Analysis report, 97% of applications now use open source components, with approximately 70% of the average codebase coming from them, and more than 900 components per application.
Open source accelerates development, but also multiplies the number of vulnerabilities that enter production environments without ever being written by internal teams.
The cybersecurity world’s trusted filter for real-world threat activity has been the U.S. Cybersecurity and Infrastructure Security Agency’s Known Exploited Vulnerabilities (KEV) list. When KEV confirms a vulnerability has been exploited, organizations prioritize it. The model is clear: verification before urgency.
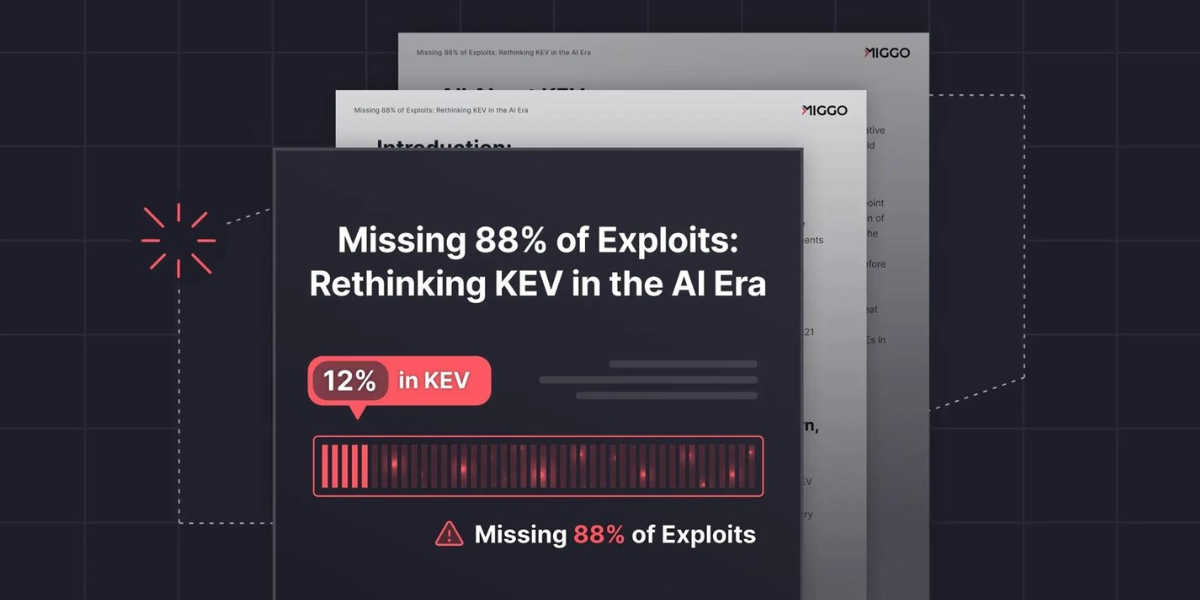
Miggo Security’s new white paper argues that this system, although well-intentioned, now hides more danger than it reveals.
Revealing a Dangerous Blind Spot
To test the reliability of KEV as a source of defensive prioritization, Miggo analyzed more than 24,000 open-source vulnerabilities from the GitHub Security Advisory (GHSA) database across ecosystems, including npm, PyPI, Maven, and RubyGems. From that dataset, the research identified 572 vulnerabilities that contained at least one GitHub-hosted exploit repository.
Only 69 of those 572 (just 12%) appear in the KEV catalog.
The details are even more striking. Four hundred seven were weaponized or functional exploits, but KEV reflected only 68; 165 were proof-of-concept exploits, but KEV reflected just one.
In other words, attackers have access to working exploit code for nearly nine out of ten vulnerabilities that most organizations would consider “not yet dangerous.”
The gap exists not because KEV is inaccurate but because KEV is confirmation-based. A vulnerability only enters KEV after exploitation has been proven. However, attackers don’t wait for validation; they leverage the exploit code the moment it is published.
This gap is exploding because AI is compressing the timeline of exploitation. According to the white paper, attackers can now weaponize vulnerabilities within minutes of disclosure, outpacing both the verification cycle and the traditional patching window.
Why Miggo Built a Predictive Vulnerability Database
Because verification cannot keep pace, Miggo maintains an independent Predictive Vulnerability Database (PVD) that continuously aggregates and classifies vulnerabilities and exploits across multiple public ecosystems, not just those appearing in KEV.
The PVD tracks not only vulnerability disclosures but also their exploitability, exploit links, exploit type, and relevance per application context. It also incorporates runtime intelligence to determine which vulnerabilities are reachable inside the customer’s software, separating theoretical risk from attack reality.
The white paper emphasizes that the PVD is not intended to replace KEV but to solve what KEV cannot: insight into vulnerabilities that are exploitable right now rather than confirmed later.
Defense Must Happen Inside the Runtime
Miggo’s report shows that even if security teams tracked every CVE and every KEV entry, the speed of AI-driven exploitation still makes legacy workflows reactive. Patching simply cannot out-run automated exploitation.
To close that window, Miggo advocates proactive runtime defense, combining runtime visibility, exploit reachability analysis, and AI-generated virtual patching. Instead of waiting for a patch or a KEV listing, runtime defense determines if a vulnerability can be exploited inside the live application and blocks the attack path instantly. This reduces the mean time to mitigation from weeks or months to seconds, allowing teams to fix securely rather than respond under pressure from an active attack.
The Metric That Matters is “Stopped Exploits”
KEV isn’t wrong. It’s just too slow for an era in which exploitation is automated. A vital statistic in the Miggo report isn’t that KEV misses 88% of vulnerabilities with known exploits. It’s what that statistic reveals: offense has begun operating faster than the entire ecosystem built to defend against it.
The future of software security will not be defined by how quickly vulnerabilities are cataloged.
It will be defined by how little time attackers have before their exploit attempts are neutralized.
And that begins not with lists, but with runtime.