By: Jacob Maslow
Accessing real-time and up-to-date news is paramount for businesses and developers in today’s fast-paced digital world. Application Programming Interfaces (APIs) have become crucial for integrating news data into projects. However, with the convenience of APIs comes the responsibility of ensuring data security. This blog will explore key security measures to implement when using APIs for news in your projects.
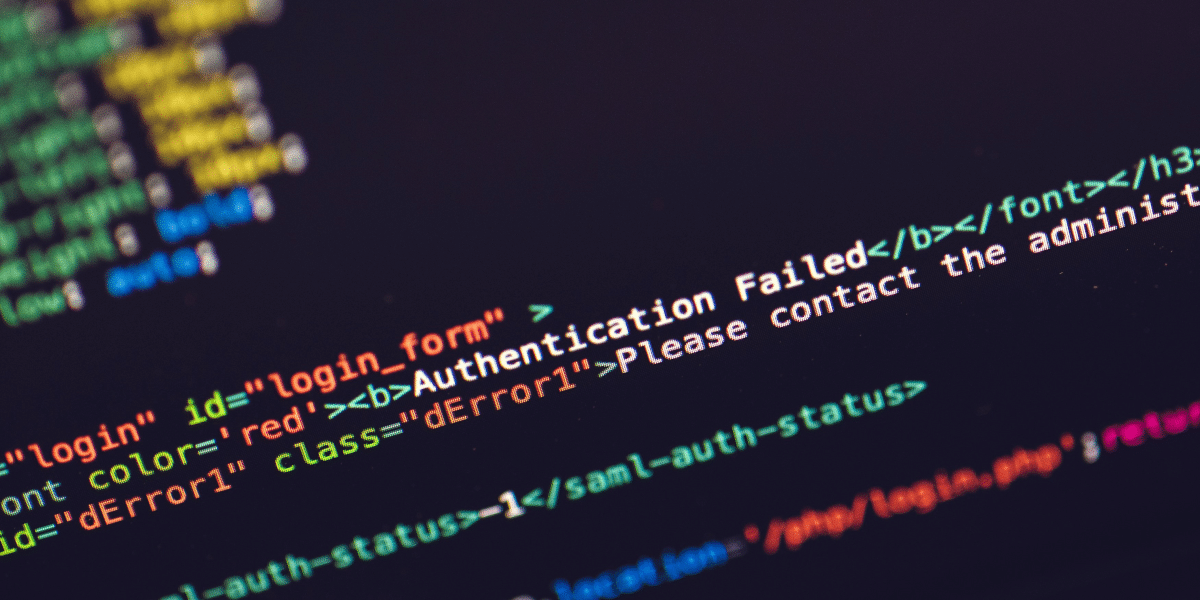
Understand API Authentication
API authentication is a vital aspect of securing your access to news data. Most APIs use authorization tokens or keys to validate applications’ requests. When utilizing APIs in your projects, it is essential to store and manage these authentication credentials carefully, especially when working with an API for news.
Implement A Secure Transmission Protocol
Securing data transmission between your project and the news API is crucial to maintaining data integrity and confidentiality. Utilizing secure communication protocols like HTTPS instead of HTTP ensures encrypted transmission channels that prevent unauthorized access or tampering during transit.
Protect Credentials at Rest
Alongside securing data transmission, it’s equally important to protect authentication credentials when stored at rest within your application infrastructure. Avoid hardcoding the keys directly into your source code, as malicious actors could easily extract them.
Regularly Update API Credentials
To enhance the security of your project using news APIs, consider rotating API credentials periodically or in case of suspected compromise. When done right, this practice helps mitigate unauthorized access risks resulting from stolen or leaked credentials.
Implement Rate Limiting
Rate limiting controls the number of API requests made over a specified time period from a specific IP address or user account associated with your project application ID. By implementing rate limiting, we can avoid excessive usage that could potentially lead to abuse or disruptive activities, causing unintended downstream impacts on on-site availability for legitimate users relying on the same news API endpoint servers operated by JSON-RP providers.
Apply Filtering and Validation Techniques
When retrieving and processing news data from APIs, ensure proper input validation to prevent data manipulation attacks such as injection or cross-site scripting (XSS) attacks. Filter user inputs to remove harmful characters or malicious code to enhance overall security.
Regular Security Scans and Vulnerability Assessments
Perform regular security scans on your project’s infrastructure, utilizing reputable vulnerability assessment tools. These scans help identify potential weaknesses in your application, its dependencies, or the underlying infrastructure so that you can promptly address them.
OAuth and Two-factor Authentication
If your application allows user authentication for accessing news within the project, it is recommended to incorporate mechanisms like OAuth and Two-factor authentication (2FA). OAuth allows secure authorization without sharing sensitive login credentials with the integrating application. 2FA adds an extra layer of security by requiring users to provide a second authentication factor apart from their passwords.
Monitor API Usage and Traffic Patterns
Closely monitoring API usage patterns can help detect abnormal activities indicative of an ongoing attack or system misuse. By establishing baseline traffic patterns, abnormal spikes or irregular trends in request volumes, response codes, or request types can be detected promptly and investigated further as necessary.
Keep APIs Updated
Keep abreast of any updates or changes the news API providers communicate—whether they are patches for bugs affecting security measures vulnerability ratings—or new versions enabling enhanced functionalities. While Improvements in new versions do not necessarily translate into direct security boosts, they may also fix loopholes that could impact overall security posture.
Final Remarks
As News APIs continue being widely adopted in various projects today, it ultimately boils down to businesses prioritizing implementation. Accessing real-time news can benefit your users. Do implement and ensure compliance with best practices around securing AppKeys. Focused on implementing strategies such as token management, protocol transmission rates, decrease possible, employing techniques, maintaining Infrastructure, applying validation procedures, and determining depth. Thoroughly complete end-to-end assessment strides information invaluable Building updates contribute pressing-induced challenges.
Published by: Nelly Chavez